The Cyber Attacks on Democracy
Fair elections are at the core of every democracy. Russia’s actions surrounding the 2016 American election were aimed at undermining the confidence of the democratic process. What can be done to prevent interference in future elections?
 Vladimir Putin, May 27, 2017 (Shutterstock.com)
Vladimir Putin, May 27, 2017 (Shutterstock.com)
The investigations into Russian meddling in the 2016 U.S. election continue to reveal a full-scale assault on the fundamentals of American democracy. From sophisticated social media efforts and traditional information operations to attempted hacks of voter rolls and state electoral systems, the Russians engaged in a concerted campaign to undermine American democracy and weaken trust in the democratic process and institutions.
This is not the only time the Russians have engaged in this kind of activity. In countries like the Netherlands, Ukraine, and France, the Russians have used influence operations to affect political campaigns, candidates, and discourse to attack perceived opponents of Putin’s Russia and support those more sympathetic to Russian interests.
The Russians have decided to use information and influence operations and cyber tools to achieve three important and complementary goals:
- To undermine faith and confidence of democracy and its institutions from within;
- To exacerbate social and political divisions advantageous to Russian interests, including in furtherance of Russian foreign policy or simply to undermine Russia’s enemies and opponents; and
- To take advantage of 21st century information environment to obfuscate or confuse the truth and amplify narratives that align with Russian interests, even when patently false.
Russia’s intent
These types of attacks – directed at the United States and other countries – certainly reveal the modern dangers and vulnerabilities to open, democratic processes, systems, and data. Russia is investing in concerted and sophisticated strategies to weaken competitor countries and weaken alliances, like NATO or within Europe, that are perceived to be aligned against Russian interests. As CIA Director Mike Pompeo noted in a recent address, Russian efforts to undermine American democracy have evolved and present a “serious threat.”
Russia is investing in concerted and sophisticated strategies to weaken competitor countries and weaken alliances, like NATO or within Europe, that are perceived to be aligned against Russian interests.
More fundamentally, they reveal a new form of combined, asymmetric influence and cyber-attacks that target democratic states and institutions. The United States and its democratic allies around the world must now treat these kinds of campaigns as fundamental, persistent, and strategic threats to the integrity of the democratic political system. They must also realize that the Russian playbook can be copied and deployed by other state and non-state actors trying to influence the course of democratic societies across the globe.
The details of the 2016 campaign are important and continue to be revealed as investigations in Congress and at the Federal Bureau of Investigation unfold, including through intelligence community findings and analyses from the Department of Homeland Security. The revealed tactics expose the Russian playbook.
The Russian campaign, which used state and non-state proxies, involved full-throated information operations through the use of traditional and social media, cyber hacks of political parties’ emails and election-related vendors, and the probing of state electoral systems and voter rolls. As a part of this campaign, up to twenty-one state election-related networks were “potentially targeted by Russian government cyber actors,” according to testimony by two Department of Homeland Security officials this summer.
The United States and its democratic allies around the world must now treat these kinds of campaigns as fundamental, persistent, and strategic threats to the integrity of the democratic political system.
The recent revelations of Russian-sponsored social media campaigns through the use of Facebook and Twitter accounts and bots (automated software to facilitate internet messaging) form part of a broader campaign by Russia to affect the political discourse in the United States, to sow social divisions, and to affect the electoral process. As details emerge, the scale of the distortion has become clearer. One estimate had the number of Twitter bots at 400,000 in the months leading up to the election. Facebook has recently turned over to Congress the details of more than 3,000 ads purchased by a Kremlin-connected company.
 Senate Intelligence Committee Vice Chairman Mark Warner (D-VA) speaks with reporters on Sept. 27, 2017. Facebook agreed to provide material to congressional investigators probing Russia interference in the 2016 election. (AP Photo/Pablo Martinez Monsivais)
Senate Intelligence Committee Vice Chairman Mark Warner (D-VA) speaks with reporters on Sept. 27, 2017. Facebook agreed to provide material to congressional investigators probing Russia interference in the 2016 election. (AP Photo/Pablo Martinez Monsivais)
It is important to understand the elements of the threat – to be able to then devise an appropriate response and defense. There are layers to the Russian campaign in the United States, perhaps adapted or emboldened when its efforts appeared to meet little resistance or seemed to be having some effect.
Though there does not seem to have been any actual cyber or other disruptions to the voting systems the day of the 2016 elections, there were attacks on state voting systems, as with the hacking of an election-service provider, and access to voting rolls, as in Illinois. The danger in such instances is the ability of foreign actors to manipulate, distort, or even destroy voting data, access, or systems. This goes to the heart of the integrity of the electoral process.
There is precedent for worrying about efforts to affect electoral results. In Ukraine in 2014, the Russians attempted to publish an electoral result that matched with their interest, which would align with manipulated voter data. Before those fraudulent results could be tabulated and announced, Ukrainian electoral officials intervened and prevented the false result from being announced. Despite this, Russian media announced the fraudulent result, which favored a candidate sympathetic to Russia.
Finally, Russia has decided to affect the underlying political debates and exacerbate fissures in societies with information operations. In Germany, Russia has exacerbated fears and tensions regarding the perceived threats from refugee populations, and in the United States, it tried to foment greater racial tension with its targeted advertisement and messaging tied to the Black Lives Matter movement in key states.
This raises the risk that a foreign actor is manipulating the political debate in crucial states on contentious issues – and at a minimum is amplifying social strife and loss of confidence in authorities and society. This is a fundamentally different kind of threat and risk.
The Russians are taking advantage of an asymmetric information and cyber environment that allows them to operate at a distance, with relative anonymity and at low cost. The cyber tools and actors to hack emails and electoral systems are readily available, the ability to use traditional media, like Russia Today, to inject stories or reinforce narratives is already established, and the ability to leverage social media in an open information environment to sow discord or confusion is relatively unchecked through Facebook, Twitter, and other online and social messaging applications.
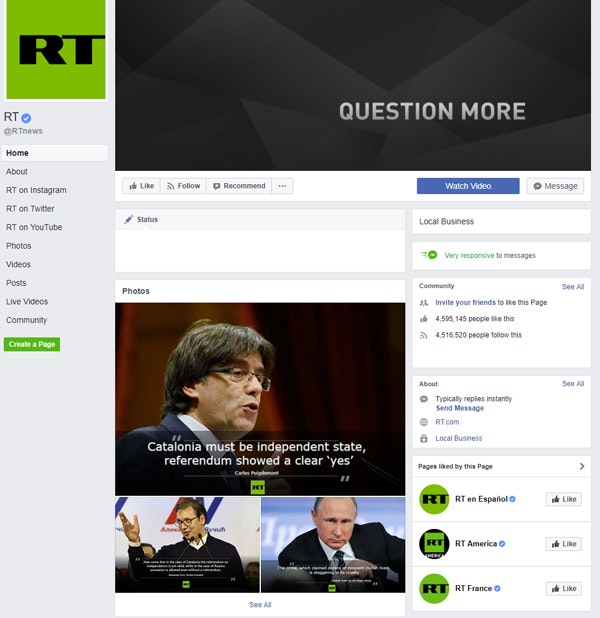 The Facebook page for <em>Russia Today</em>, October 16, 2017.
The Facebook page for <em>Russia Today</em>, October 16, 2017.
The nature of these campaigns – asymmetric information operations and cyber attacks that reinforce each other and put democratic systems at risk – play to the Russian strength of leveraging state and non-state actors to deploy their campaigns. The great danger is the loss of faith and confidence in the electoral system, democratic processes, and leadership.
Even if the Russians or other foreign actors were not able to manipulate voting patterns, machines, or electoral results, the mere act of undermining confidence in institutions, leaders, and democracy would be a strategic objective unto itself. This alone may be a design of any campaign – simply to sow distrust and heighten cynicism in the democratic process.
This alone may be a design of any campaign – simply to sow distrust and heighten cynicism in the democratic process.
Responding to cyber threats
A series of complementary steps need to be taken to defend against and confront this new type of threat:
Clarity, Credibility, Closure on Russian Investigations
The various investigations underway regarding Russian meddling need to stay focused on understanding how the Russians attempted to affect or influence the election. This requires clarity and credibility in the findings – from Congress and Special Counsel Robert Mueller. This also requires closure to help restore confidence in the system. Understanding the tools and tradecraft of Russia and its proxies will help the United States and its allies create collective awareness and counter such campaigns in the future.
Defense and Redundancy of Current Systems
There needs to be a comprehensive review of the security and redundancy of the national electoral system, now considered a critical national infrastructure. Though the electoral system is run at the state and local levels, there needs to be a complete review of how the “supply chain” of the electoral process is protected – from integrity of voter rolls to the security of voting machines, software, and results.
The advantage of the current, distributed system is that one attack is not sufficient to jeopardize the entire system. Additional security may include keeping core electoral systems distributed and even off-line, the use of paper ballots as necessary front-line or back-up systems to machine-based voting systems, and ensuring there is redundancy for voting processes to allow for voting to continue if parts of the electoral system are downed or compromised the day of elections. These systems need to be tested before the next election to ensure gaps are identified and defenses are as secure as possible.
Funding Transparency
Given the ability of Russia and other foreign actors to fund and influence elections, campaigns, and parties in open systems, there needs to be greater, more rigorous transparency in campaign funding and reporting. This should also include immediate adoption of beneficial ownership and corporate formation requirements that would make the ownership of shell companies in the United States transparent.
This would avoid the possibility of foreign actors forming U.S. companies for the purpose of funding or supporting political campaigns or processes. Such efforts should also include more open monitoring of the purchase of advertisements and the funding of social media campaigns intended to influence political processes. The recently-introduced DISCLOSE Act of 2017 would prohibit domestic corporations with significant foreign control, ownership, or direction from spending money in U.S. elections.
Information Validation
The trickiest challenge in this new world of open and global information is how to ferret out false stories or “fake news” that are being used to drive campaigns to undermine U.S. and other democracies. Who determines truth or validity, and how best can news outlets and social media platforms identify, label, and exclude “fake news”?
In the face of fake news and dangerous narratives constructed by Russia, European countries and agencies have established centers to counter fake news, by identifying and pushing back on false stories and narratives as they appear. In the Czech Republic, for example, a unit was established to discover and counter inaccurate information and fake news, particularly any tied to Russia.
Twitter and Facebook are now grappling with how best to address this challenge, by flagging false news and perhaps moving to a better-business-bureau-like model to validate stories and information. At a minimum, countries affected by false narrative assaults can create mechanisms in the public and private sector to counter the ideas and reveal their falsity and origins.
Deterrence
To date, there has been relatively no cost to this kind of asymmetric information and cyber campaign from Russia. That needs to change if we hope to defend against a flurry of these kinds of attacks again from Russia and others. Other than new sanctions passed by Congress to address Russian cyber activity, very little has been done to counter this type of campaign.
In the first instance, there needs to be clarity – declared publicly by the Executive Branch – that attacks on the U.S. electoral system will be treated as would other cyber attacks or threats on our infrastructure and that the United States will respond – proportionately and in the manner and timing of our choosing. There needs to be a campaign to reveal the sources and methods of Russian and other meddling in the U.S. electoral system – mapping where Russian money and influence are dotting the electoral landscape.
There needs to be clarity – declared publicly by the Executive Branch – that attacks on the U.S. electoral system will be treated as would other cyber attacks or threats on our infrastructure and that the United States will respond – proportionately and in the manner and timing of our choosing.
The U.S. and European Union should impose new types of sanctions together against actors attempting to influence and undermine democratic systems and processes outside the bounds of the law. This would involve public exposure of those individuals and entities involved, and the freezing of their assets and locking out of the Western financial and commercial system.
Finally, the United States should work with state, local, and private sector entities to explore what coordinated active defense models might look like as a way of dynamically responding to malware and cyber attacks that attempt to compromise the electoral system. The fact that active defense measures – of a variety of sorts – could be employed should be communicated and form part of a deterrence strategy.
The Russian attacks on the U.S. electoral system and processes have revealed a bolder strategy and set of vulnerabilities to the democratic system. These are threats not just from Russia and not just targeted at the United States. This is a new form of asymmetric influence and warfare, which needs to be treated as a strategic threat to the United States and its democratic allies.
The Catalyst believes that ideas matter. We aim to stimulate debate on the most important issues of the day, featuring a range of arguments that are constructive, high-minded, and share our core values of freedom, opportunity, accountability, and compassion. To that end, we seek out ideas that may challenge us, and the authors’ views presented here are their own; The Catalyst does not endorse any particular policy, politician, or party.
-
Previous Article America’s Democracy Is Not in Danger, but This Is No Cause for Complacency An Essay by William A. Galston, Senior Fellow at The Brookings Institution and Columnist for The Wall Street Journal
-
Next Article Condoleezza Rice: Why Democracy is Worth the Effort A Conversation with Condoleezza Rice, Former U.S. Secretary of State

